[ad_1]
Bettering effectivity for the Cisco staff within the Black Hat USA NOC
As a proud associate of the Black Hat USA NOC, Cisco deployed a number of applied sciences together with the opposite Black Hat NOC companions to construct a secure and safe community for the convention. We used Cisco Safe Malware Analytics to investigate recordsdata and monitor any potential PII leaks. We additionally used Meraki SM to handle over 300 iPads used across the venue for registration, in addition to gross sales lead technology. Final however not least, we used Umbrella so as to add DNS stage visibility, risk intelligence and safety to your complete community.
Lets go over an instance situation which many purchasers might discover themselves in. Whereas we have been within the Black Hat USA NOC (take a look at this weblog about Cisco Safe within the NOC), we have been consistently retaining our eyes on the Umbrella safety exercise report, with a purpose to acknowledge, examine and work with different groups to reply to the threats.

Repeatedly monitoring the exercise report might be taxing, particularly in our case with two Umbrella organizations – one for the convention iPad deployment and one other for the convention attendee community. In comes SecureX to assist make our lives less complicated. Utilizing SecureX orchestration we have been capable of import a pre-built Umbrella workflow and simply customise it to suite our wants. This workflow pulls the exercise report for a configurable listing of classes, creates an incident in SecureX, notifies the staff in Webex Groups and updates a SecureX dashboard tile. Let’s bounce into SecureX orchestration and check out the workflow.
A plethora of SecureX orchestration content material is accessible on our GitHub repo that can assist you discover worth in our automation engine very quickly. On the hyperlink above, you’ll discover totally constructed workflows, in addition to constructing blocks to craft your individual use circumstances. Here’s what the 0023 Umbrella: Extreme Requests To Incidents workflow appears like upon importing it (shoutout to @mavander for authoring the workflow).

You may see within the variable part there are 4 variables, three strings and one integer. “Classes to Alert On” is a comma separated listing of classes we need to be notified about, which makes it very straightforward so as to add or take away classes on the fly. In our case, we need to be notified if there’s even one DNS request for any of the Safety Classes, which is why we have now set the “request threshold” to 1.

Now that our variables are set, let’s dig into the primary internet service name that’s made to the Umbrella API. Umbrella has three API’s:
- The administration API
- The Examine API
- The reporting API (which is the one we have to use to drag the exercise report)
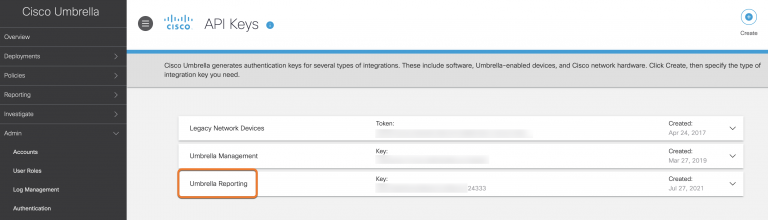
There are sometimes minute variations when authenticating to numerous API’s, however fortunately for us, authenticating to the Umbrella API is constructed into the workflow. It’s so simple as copying and pasting an API key from Umbrella into orchestration and that its. You’ll discover the Umbrella API key and secret are saved as ‘Account Keys’ in orchestration this fashion you’ll be able to reuse the identical credentials in different workflows or different API calls to Umbrella.

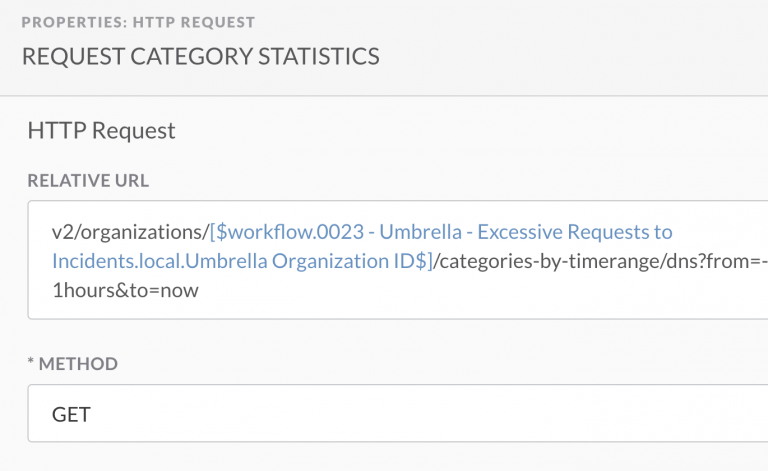
On this case, we’re dynamically crafting the URL of /v2/organizations/<umbrella_org_id>/categories-by-timerange/dns?from=-1hours&to=now by utilizing the Umbrella org ID from the variables above. Discover the API name goes to GET an exercise report for the previous hour, nevertheless it might be modified to be kind of steadily.
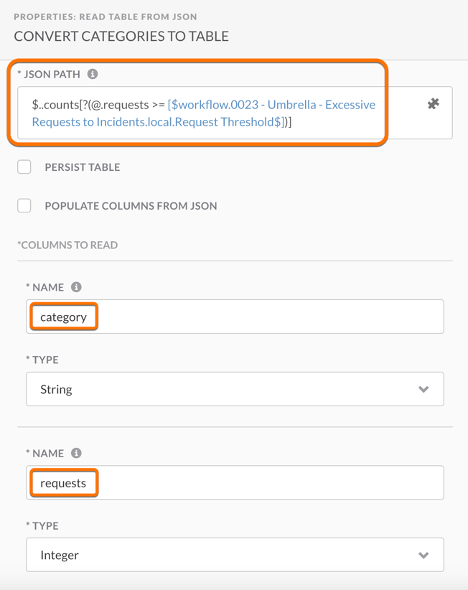
Now that we have now a JSON formatted model of the exercise report, we are able to use JSON path question to parse the report and assemble a desk with the class names and the variety of requests. Utilizing this dictionary, we are able to simply decide if Umbrella has seen a number of requests for a class which we need to alert on.
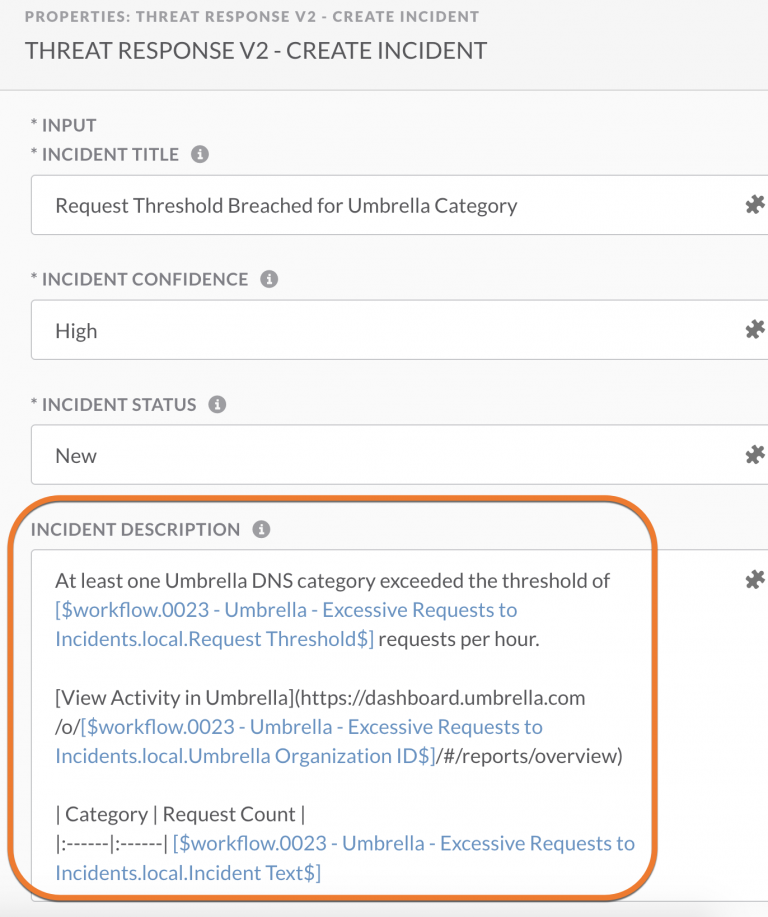
If the situations are met, and there was exercise in Umbrella, the workflow will mechanically create a SecureX incident. This incident might be assigned to a staff member and investigated in SecureX risk response, to achieve further context from numerous intelligence sources. Nevertheless, our staff determined that merely creating the SecureX incident was not sufficient and {that a} extra lively type of notification was essential to make sure nothing received neglected. Utilizing the pre-built code blocks in SecureX orchestration, we personalized the workflow to print a message in Webex groups this fashion the entire staff might be notified and nothing will go unseen.

Here’s what the message appears like in Webex groups. It contains contains the title of the class and what number of requests in mentioned class have been seen previously one hour. We scheduled the workflow to run as soon as an hour, so this fashion even when we wanted to step away to stroll the Black Hat ground or meet with a NOC associate, we are able to nonetheless keep abreast to the newest Umbrella detections.

It additionally features a hyperlink to the SecureX incident to make the following step of conducting an investigation simpler. Utilizing SecureX risk response we are able to examine any domains detected by umbrella to get reputational information from a number of intelligence sources. On this specific instance www.tqlkg[.]com confirmed up as ‘probably dangerous’ within the Umbrella exercise report. The outcomes of the risk response investigation present tendencies from 5 totally different sources together with a suspicious disposition from each Talos and Cyberprotect. We are able to additionally see that the area resolves to six different suspicious URLs. In a future model of this workflow this step might be automated utilizing the SecureX API’s.

Along with the Webex groups alert, we created a tile for notification the SecureX dashboard, which is on show for your complete NOC ground to view.

You may see within the dashboard excessive stage statistics, that are offered from Safe Malware Analytics (Risk Grid) together with “prime behavioral indicators”, “submissions by risk rating” “submissions by file sort” in addition to the “request abstract” from Umbrella.
Additionally discover the “personal intelligence” tile – that is the place you’ll be able to see if there have been any new incidents created by the orchestration workflow. The SecureX dashboard retains your complete Black Hat NOC well-informed as to how Cisco Safe’s portfolio is working within the community. Including tiles to create a customized dashboard might be achieved in only a few clicks. Within the customise menu you will notice all of the built-in applied sciences that present tiles to the dashboard. Beneath the “personal intelligence” part you’ll be able to see the choice so as to add the ‘Incident statuses and assignees’ tile to the dashboard – it’s that straightforward to create a personalized dashboard!

I hope you loved this version of SecureX at Black Hat; and keep tuned for the following model of the workflow on GitHub, that may mechanically conduct an investigation of suspicious domains and supply intelligence context immediately within the Webex groups message.
We’d love to listen to what you suppose. Ask a Query, Remark Beneath, and Keep Related with Cisco Safe on social!
Cisco Safe Social Channels
Share:
[ad_2]