[ad_1]
Now we have spent many of the final couple of many years serving to massive
organizations overhaul their legacy methods. In doing this we have realized a
nice deal about what works and seen many paths that result in failure. We have
determined to put aside a while to writing down what we have realized within the kind
of varied patterns that we have seen used.
This text acts because the hub for these patterns. Too typically we have seen
organizations caught on a treadmill of half-done legacy substitute efforts. We
assume the important thing to breaking this cycle requires 4 actions accomplished considerably in
sequence however largely iteratively over an organization’s life. We use these actions
as our major construction for organising the patterns that we describe.
We have all the time believed that efficient software program improvement entails gradual
launch of worthwhile options, and we predict the identical is true of writing –
particularly within the age of the
internet. We have began with this narrative article and can regularly
add patterns as we write up their particulars, in addition to different examples that present
how they mix. We won’t promise any dates, since our precedence is our consumer
work, which isn’t wanting legacies to displace. In case you are excited by
listening to about extra components of this work as they seem, they are going to be introduced
on Martin’s twitter feed,
and this web site’s RSS
feed.
The Legacy Substitute Treadmill
Now we have labored with many organizations who’ve made a number of makes an attempt at
eradicating legacy methods. In a single pretty typical group
they’d been by an entire collection
of 3-5 12 months lengthy modernization programmes. Every time they might outline a brand new
tech strategy, after which work in direction of that new strategy as half of a giant
multi 12 months modernization programme.
Sooner or later throughout every programme they hit a disaster level the place altering
enterprise wants would overtake their present tech technique and therefore set off
the necessity to begin over. The place they’d taken a waterfall “huge bang” strategy to the
programme this meant abandoning the vast majority of the work. In different circumstances
with extra incremental supply approaches, the strategy taken was to only add a
layer of barely newer applied sciences on high of an already complicated
panorama. For each situations they have been unable to decommission any of their
legacy stack, key enterprise targets for price financial savings and threat discount remained
unmet, an all too frequent consequence for a lot of legacy substitute efforts.
A number of key elements have been in play of their repeated failures.
Firstly the poor outcomes they have been seeing have been largely a product of
the group; particularly it is management, construction and methods of working.
They thought by simply choosing newer applied sciences, however leaving all the things
else roughly unchanged, that they might get totally different outcomes from the
previous. In hindsight this was clearly unrealistic.
Secondly the modernization was to be delivered by a big change programme,
itself comprising a collection of initiatives and groups. These initiatives have been handled
as orthogonal to any BAU (Enterprise As-Traditional) efforts. So BAU supply of enterprise necessities
continued towards the present methods whereas the brand new challenge groups delivered
towards a set of necessities agreed at the start of the substitute
programme.
Over time they noticed a widening hole between what the enterprise truly
wanted and what was truly signed off firstly of the programme. The longer every
programme ran for, the extra acute this hole between the programme plan
vs. BAU and future wants. Whereas change management processes have been
in place so as to add new necessities to a programme, these have been massively
time-consuming and, resulting from upfront provider contracts, prohibitively costly.
A 3rd key think about a number of of the failures was the will for
Characteristic Parity with the present set of methods and enterprise processes.
These makes an attempt started by promising to provide the enterprise precisely what they
had immediately with someway, behind the covers, the expertise having been
“improved”. Having by then seen a number of failures and worrying about
disruption, the enterprise leaders felt this was a decrease threat technique.
The problem right here was even defining and agreeing present “as is”
performance was an enormous effort and it led to a plan for a big single
“huge bang” cut-over launch.
Our observations from this and lots of different organizations is that
expertise is at most solely 50% of the legacy downside, methods of working,
group construction and management are simply as necessary to
success.
Breaking the cycle
Clearly there’s a want to interrupt out of the cycle of “expertise substitute
programmes”. In brief organizations want to have the ability to proceed to ship
enterprise wants whereas on the similar time changing outdated expertise, all
towards a background of accelerating technological change and a harder
aggressive local weather.
There are a collection of approaches we now have discovered might help with these challenges.
They assist with the problem of breaking the issue into smaller components to
enable supply of latest necessities in parallel with improved expertise.
Broadly talking they match into 4 classes:
- Perceive the outcomes you need to obtain
- Determine how you can break the issue up into smaller components
- Efficiently ship the components
- Change the group to permit this to occur on an ongoing foundation
Perceive the outcomes you need to obtain
It is important for a corporation to agree the outcomes they need to
obtain when tackling legacy. Whereas this may increasingly appear apparent, all too typically
totally different components of a corporation can have fairly totally different views on the
desired outcomes. Most legacy modernization initiatives contain a number of of
the outcomes we listing beneath, however it’s important to determine which of them are
the precedence earlier than setting out on the journey.
Lowering the price of change
A key tipping level in lots of organizations in deciding to sort out legacy is
that desired enterprise modifications begin to price excess of any anticipated
advantages, both resulting from alternative price (aka delay) or implementation price.
An early warning signal is having to spend weeks and 10’s or 100’s of hundreds
to make a change to a web site that brings solely a small improve in enterprise
efficiency.
At this level it’s typically now not potential to justify making
any modifications that do not ship massive returns on funding. In different
phrases the state of the expertise has began to dictate the dimensions of change
the enterprise could make. For a lot of organizations this implies the distinction
between making a ‘BAU’ change or having to instigate a bigger challenge.
These bigger initiatives then grow to be magnets for all of the small modifications
that weren’t beforehand justifiable thus rising their scope, price
and threat
Bettering the enterprise course of
Now we have seen numerous examples of the place enterprise processes have developed
subsequent to legacy methods, the processes grow to be tightly coupled to the
approach that system works with constraints within the system and sometimes workarounds “off system”
shaping the enterprise processes folks comply with to do their jobs.
One instance we noticed is an airline check-in system that used “inexperienced display screen”
terminals, resulting from constraints within the legacy system the method needed to
be adopted in a strict order that means corrections or errors meant
beginning the check-in course of over. Additionally initially the airline had
not supplied connecting flights, when this was added it needed to be accomplished
as a separate workflow within the legacy system resulting from constraints in that
expertise. So if, at check-in, a passenger didn’t point out
they’d a connecting flight the improper course of was adopted
together with printing the improper baggage tags, solely after this is able to the
system flag the connecting flight. The roles of the check-in workers and
the passenger’s expertise might have been a lot improved by altering
the method, however this was inconceivable as a result of legacy system.
Given this it needs to be no shock that to replace and alter enterprise
processes in flip requires modifications to the how the supporting expertise works.
Attempting to alter working processes with out altering the expertise typically
ends in “off system” working the place folks resort to extracting knowledge
into spreadsheets or comparable, engaged on it there, earlier than importing the
knowledge again into the legacy system.
In a single group the entire inventory ordering course of was truly accomplished
on a Microsoft Entry DB operating on the staff managers PC. That they had
grow to be pissed off because the legacy system couldn’t help the
newer working practices of their suppliers. They might do an import
and export of the info just a few occasions per week, within the meantime the remaining
of the group would see outdated figures as nobody realized
what was happening.
It’s price noting right here that necessities for a substitute system to
help import and export of knowledge can typically have a root trigger on this
type of workaround.
Retire an previous system
The necessity to retire an previous system is a typical cause for legacy modernization.
That is typically pushed by challenges in supporting older {hardware} or software program,
with points reminiscent of escalating help prices and reaching end-of-life
on help contracts for each {hardware} and software program.
We have discovered it helpful to view the retirement of previous methods by the lens of
the enterprise. So a system being constructed on previous expertise will not be in of itself
ample cause for substitute. As a substitute we have to take a look at the enterprise
influence this creates such escalating run prices or the danger created by lack of
help or information of the system.
Whereas some organizations do plan properly for obsolescence of older applied sciences,
many appear to disregard the problem till it reaches disaster level. In flip, this
tends to drive organizations in direction of modernization approaches that appear like
low disruption choices or fast wins, these are normally anti-patterns
and we describe a few of these pitfalls later.
We have been shocked over time at what number of massive organizations are
operating their companies on unsupported {hardware} and software program, shopping for
spare components on eBay is surprisingly frequent story to listen to. If in case you have
legacy tech it’s properly price doing a correct survey and making a calendar
that includes the varied end-of-life help dates.
Whereas many organizations give retirement of previous methods as a key consequence
for legacy modernization it’s not unusual to search out this does not truly
occur, the legacy remains to be getting used on the finish with the related
enterprise targets remaining unmet.
Imminent Disruption
For some organizations the precise tipping level on tackling legacy can
come up resulting from an exterior issue reminiscent of a regulatory change, a brand new “begin up”
competitor or a big change by an current competitor. It is typically
at this level when confronted with a “should do” change it turns into clear the cash
and the time required to reply has grown too massive.
The exterior occasion is the factor that makes clear to a corporation’s
management that they now not have the flexibility to make modifications for a
Proportionate Value.
Newer expertise
Adoption of newer expertise shouldn’t be the rationale for legacy
modernization, simply having newer tech for it is personal sake isn’t a
key purpose for any group. Reasonably it needs to be chosen and chosen in
ways in which finest meet the present and future wants of the enterprise. A problem
right here is that tempo of technological change is accelerating, the “helpful”
lifetime of expertise is getting shorter. The precise definition
of “helpful” is determined by the group, however basically we have to
contemplate issues reminiscent of:
- Permits a aggressive benefit
- Match competitor or market choices
- Permits a Quicker tempo of change
- Cheaper to alter
- Has a decrease run price
The alternatives we make immediately about the very best and most helpful expertise will
seemingly be overtaken by higher alternate options in a comparatively brief timeframe.
This makes getting the choice proper on discovering expertise to satisfy future
wants doubtlessly very dangerous.
A superb strategy right here is to not make any decisions that can’t simply be
“accomplished over” with 2-3 years. This has implications for each expertise
choice but additionally for total design and strategy. Deciding on an enormous
platform with a 5-10 years pay again time is difficult to justify once we
acknowledge this accelerating tempo of change.
Determine how you can break the issue into smaller components
Broadly talking this entails discovering the precise “seams” within the present
enterprise and technical structure. Importantly, you must contemplate how
parts of the present resolution map to totally different enterprise capabilities. For
legacy methods this normally means discovering how one massive technical
resolution meets a number of enterprise wants after which seeing whether it is potential
to extract particular person wants for impartial supply utilizing a brand new resolution. Ideally these
needs to be deliverable with minimal dependencies on one another.
A typical objection is that discovering these seams is simply too tough. Whereas we
agree it’s difficult at first, we now have discovered it to be a greater strategy than
the alternate options which all too typically end in Characteristic Parity and Massive Bang releases.
We have additionally noticed that many organizations rule out such an strategy as a result of
they’re wanting on the expertise, or the enterprise processes, in isolation.
Altering only one a part of the expertise, or updating only one enterprise
course of independently is more likely to fail, but when we will contemplate after which
implement the 2 collectively there are methods to “eat the elephant”.
Getting Began
Legacy modernization can appear a most daunting proposition firstly of the journey. Like several journey, we
should first try to perceive the preliminary path to take. Additionally, like all journeys, you could begin from
the place you might be. One frequent downside we encounter is that we frequently appear to start out in a forest with no view of the
panorama forward and subsequently no thought of the path to take. Step one, then, is to climb a tree and
take an excellent go searching! This implies getting pretty much as good an understanding of the present methods and structure
as potential within the shortest period of time. That is typically tremendous laborious to do and it is simple to get slowed down in
an excessive amount of element.
Thankfully there are a selection of actually helpful instruments that can be utilized collaboratively
to get a ok understanding to proceed. These instruments are mentioned
intimately elsewhere however a abstract listing would come with
Occasion Storming,
Wardley Mapping,
Enterprise Functionality Mapping and Area Mapping.
Discover on this listing that we’re primarily how enterprise ideas
are mapping into the methods structure, and in flip understanding
how that
structure helps worth era.
It is a view that’s typically lacking particularly for legacy methods.
| Worth Stream Map † | Artefact that describes how customers accomplish their work |
| Occasion Storm † | Method used to grasp enterprise processes |
Particularly we discover folks typically cease discovery type actions on the
boundaries of the legacy methods, “right here be dragons”, go no additional.
With out crossing the boundary and uncovering how legacy methods help
(or hinder) enterprise course of and actions it’s difficult to search out
and extract skinny slices to ship.
One other oft ignored and really worthwhile supply of data are the customers of the methods themselves. In
truth, within the authors expertise that is typically the place you will discover the stunning quantities of helpful stuff and
particularly expose the numerous workarounds and shadow IT ecosystem that normally builds up round older methods –
that’s, the Entry Databases and versioned Excel Spreadsheets that truly run the enterprise. Buyer
Journey Mapping, creating Service Blueprints and Worth Stream Mapping are instruments which have been used to good impact
to floor this sort of element.
Efficiently ship the components
The necessity for sooner change and the flexibility to incrementally ship and
independently change parts of the enterprise with out massive dependencies typically
results in “agile” supply approaches alongside a microservices primarily based structure.
Steady Supply turns into a will need to have for these individually deployable elements.
What makes this difficult past only a regular piece of software program supply is discovering
methods for reduce over from, co-existence with and, in the end substitute of
parts of an current massive resolution. A number of profitable methods exist
together with parallel run, fork on ingress and diversion of movement.
| Canary Launch † | Roll out a change to a subset of customers |
| Cease the World cutover † | Droop regular enterprise actions whereas reducing over to new system |
| Revert to Supply † | Determine the originating supply of knowledge and combine to that |
| Divert the Circulation † | Divert key enterprise actions and processes away from legacy first |
| Darkish Launching † | Name a brand new again finish characteristic with out utilizing outcomes in an effort to assess its efficiency influence. |
| Legacy Mimic † | New system interacts with legacy system in such a approach that the previous system will not be conscious of any modifications. |
| Occasion Interception † | Intercept any updates to system state and route a few of them to a brand new part |
Change the group to permit this to occur on an ongoing foundation
If we step again and take a look at the entire means of delivering new enterprise
necessities we will shortly see that is solely partly a expertise downside. If
we use newer expertise to chop time and value of constructing options we are going to
then spotlight any points round agreeing necessities and getting the change
into manufacturing.
We’d like group construction and course of modifications to take
full benefit of the higher expertise, and by “Conway’s Regulation” we
additionally want an structure for our expertise that facilitates this. If
groups and their communications are organized across the current legacy
resolution and processes we might must reorganize them utilizing the
Inverse Conway Maneuver to match the brand new
resolution and it is structure.
Legacy methods can constrain and restrict the flexibility to undertake extra
fashionable engineering practices particularly these related to eXtreme
Programming and Steady Supply. When changing legacy methods it
is necessary to verify methods of working are modified to make sure we
do not find yourself again with a system that’s gradual, tough and costly
to alter.
Legacy can be the product of an organizations
tradition and management, with out broader change it is best to count on the
similar outcomes as seen beforehand.
Now we have noticed many legacy modernization efforts fail resulting from
“company antibodies” which spot one thing new taking place and act to
reject it from the group.
To present only one instance of the best way a broad group can reject
change; we labored with a really massive telecommunications firm who needed
to construct software program for cellphones. The management all understood this
meant a lot sooner suggestions cycles and extra frequent modifications than they
noticed with current programmes which have been targeted on fastened infrastructure.
Whereas the management understood this no modifications have been made to current
working follow or to the center administration who ran these processes. So
current change management processes have been rigorously utilized. In the long run
the software program groups have been spending extra time filling in change management
varieties and attending change management conferences than they have been producing
software program. The “company antibodies” labored efficiently to reject the
new approach of working.
Organizational change is a giant subject with a lot literature already accessible,
the important thing problem with legacy is usually time associated. Few organizations can
afford to delay legacy modernization whereas they rework (or rebuild, for
outsourcing victims) their complete supply strategy alongside facet their
group construction and key enterprise processes. Whereas the broader subject
of group transformation is past our scope we do advocate some
methods for making use of and defending new methods of working within the context of
legacy. In case you simply change the legacy and do nothing else it’s honest to
count on you may changing legacy once more with just a few years.
| Begin as you imply to proceed † | Create your legacy substitute in the best way that you must proceed as soon as it’s dwell. |
| Protected Pilot † | Create a pilot program for brand new work and detach it from the traditional company governance course of |
| New Co † | Type a model new firm to pursue a market disruption |
There are positively different methods and approaches to group
transformation, we simply highlighted these two as to some extent they
enable work to be began on the legacy modernization sooner slightly than
later.
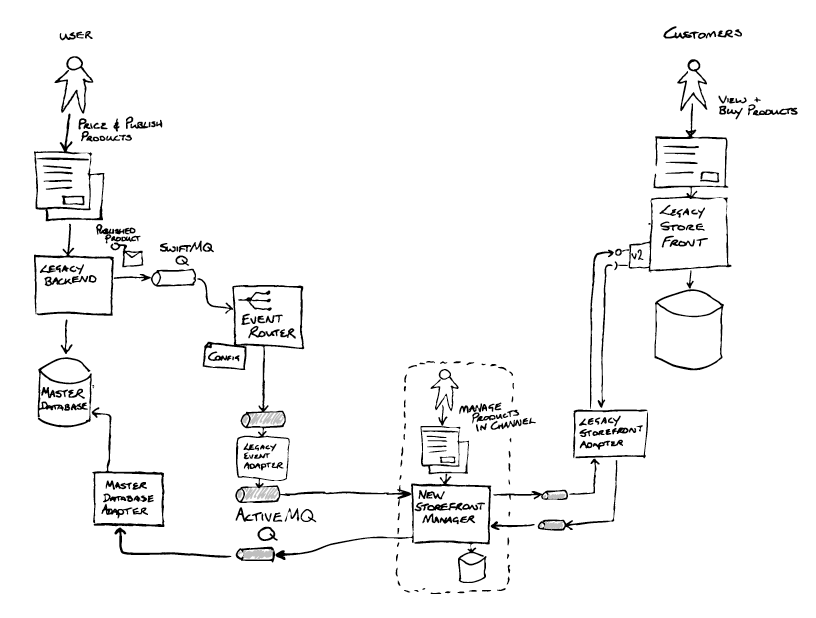
An instance: Integration Middleware Removing
This instance describes how certainly one of our groups used numerous Legacy
Modernization Patterns to efficiently change integration middleware
vital to the operation of their consumer’s enterprise as half of a bigger
legacy modernization programme. They mixed patterns and refactorings to
efficiently handle threat to the enterprise, and facilitate consuming this
significantly gristly a part of the elephant.
Understanding the outcomes
The problem confronted by our staff was how you can change integration middleware
that was out of help, laborious to alter and really expensive with a brand new
supportable, versatile resolution for the enterprise. With out disrupting or
placing in danger current enterprise operations. The middleware in query was
used to combine between a backend finish system and a retailer entrance. Collectively
these methods have been accountable for promoting excessive worth distinctive merchandise price
tens of hundreds of thousands of kilos on daily basis.
This work was a excessive precedence half of a bigger programme. Everything of
the backend methods supporting the enterprise have been being changed, and the
retailer entrance was additionally going to be topic to a modernization programme inside
a few years.
So, as per step 1 above, the enterprise outcomes the staff wanted to attain have been outlined:
- Enhance the enterprise course of
- Retire previous system as quickly as potential
How? This specific integration middleware resolution contained a big quantity of logic together with guidelines
core to the enterprise, like which channel to promote a product on, or how and when to current a product on the market
throughout the retailer entrance. This current system was very laborious to alter, stifling enterprise innovation, and flaws
within the logic resulted in points like having durations when a product was not even on sale!
Why? To scale back current (and rising) license and help prices. Moreover, to mitigate the danger to
the enterprise created by working vital features on aged out of help middleware and database
applied sciences.
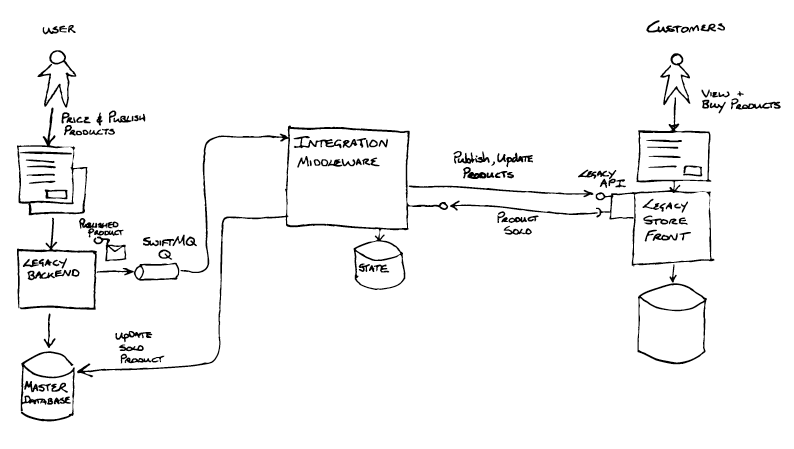
Breaking the issue up: the primary seam and a refactoring
Throughout Inception the staff ran a workshop
with individuals who had deep information of the legacy system, to collaboratively
visualise each the as-is and to-be software program architectures.
Having accomplished this, they discovered a technical seam that could possibly be exploited in
the type of messaging primarily based integration between the legacy backend and the Integration
Middleware. The Legacy backend, an getting older J2EE software, positioned “publish product” messages
onto a queue supplied by a really previous model of SwiftMQ. The Occasion Interception sample can be helpful right here,
and if applied as a Content material-Primarily based Router
would enable management over how messages from the legacy backend have been routed,
and create an possibility enabling messages to be routed to new methods.
The combination middleware additionally dealt with messages coming from the Retailer
Entrance (e.g. for product gross sales), utilizing JDBC to immediately replace state within the
Grasp Database behind the legacy backend. Collectively the asynchronous
messaging by way of SwiftMQ and the JDBC database updates shaped the interface
between the Legacy Backend and the Integration Middleware.
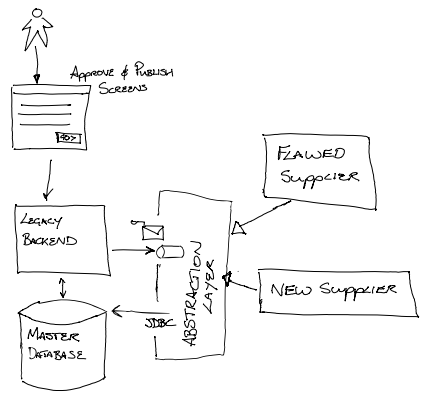
Though, not noticed on the time, the staff have been ready to make use of the Department by Abstraction sample, at a sub-system scale, as
the technique to allow the substitute of the legacy middleware. The
abstraction layer being the queues and the JDBC. By guaranteeing that the brand new
implementation adhered to that abstraction layer it could possibly be swapped for the
“flawed provider” with out impacting the enterprise operations.
The very first thing the staff did was to implement occasion interception by
including an Occasion Router by way of a refactoring.
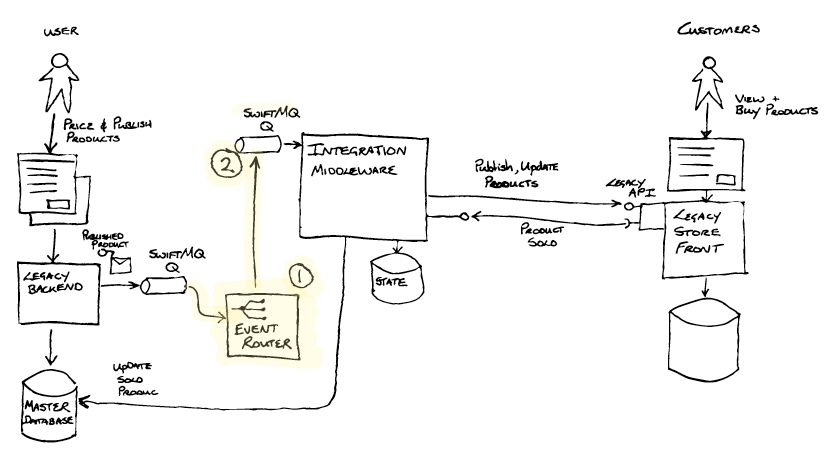
The Occasion Router (1) was created with three important capabilities in
thoughts:
- To de-queue messages from one SwiftMQ queue and en-queue them onto
one other SwiftMQ queue (2). A trivial change of some config enabled the
Integration Middleware to eat messages from this new queue(2). - The imaginative and prescient for the Occasion Router was to allow, by configuration,
routing of messages to another vacation spot – enabling the brand new
implementation to course of the publish messages. Occasion Interception - The Occasion Router would additionally present a bridge from the previous SwiftMQ
expertise to the brand new ActiveMQ expertise chosen for the goal
structure.
General the refactoring left the observable system behaviour unchanged,
however the Occasion Router was now a part of the Transitional Structure,
having been inserted into the message processing pipeline.
Implementing the Occasion router was not as straight ahead because it might
have been. Integrating with SwiftMQ was problematic resulting from lack of obtainable
drivers / libraries and the strategy was challenged numerous occasions. The
staff understood the worth of the choices that this strategy would unlock,
and accomplished the work and launched into manufacturing. They monitored the brand new
part within the wild and have been set to incrementally improve its functionality
utilizing new Steady Supply pipelines.
Efficiently ship the components: constructing out the performance, sustaining the contract
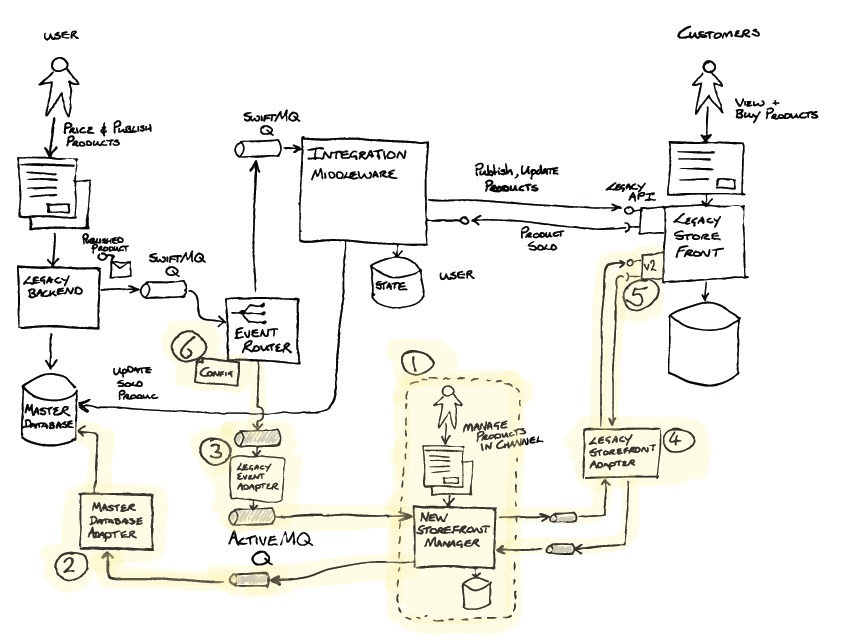
The brand new Retailer Entrance Supervisor(1) was now iteratively constructed out by the staff
. Related to this instance, that construct included the Grasp Database
Adapter (2) implementing the Legacy Mimic sample. This was required as half
of the abstraction layer, to replace the Grasp Database with gross sales
data obtained from the Retailer Entrance. Because the Occasion Router didn’t
remodel messages, a Legacy Occasion Adapter (3) (Message Translator) was created to remodel messages
into a brand new format, not exposing the legacy world to the brand new, and aligning to
the ideas of the brand new structure. The Legacy Storefront Adapter(4) was additionally applied between the brand new Retailer
Entrance Supervisor(1) and the Legacy Retailer Entrance to isolate the brand new
implementation from future modifications that might be coming when the shop entrance
was changed.
A brand new API was launched on the Legacy Retailer Entrance (5) that the brand new Retailer
Entrance Supervisor was to make use of. Moreover, a characteristic was added enabling name
backs for merchandise revealed on the brand new API to be despatched to the brand new Retailer
Entrance Supervisor’s adapter (4). Critically, this enabled the legacy
implementation and the brand new implementation to be run in parallel.
Efficiently ship the components (cont.): transitioning into dwell service – utilizing a second seam
With all the items in place the enterprise have been in a position to take a look at the brand new
resolution, however how you can roll it out into dwell service in a threat managed approach.
To do that they took benefit of one other seam – this time utilizing the
Section by Product sample. The Occasion Router was enhanced so as to add
configurable routing (6) by product sort in addition to by distinctive
product IDs. The staff have been in a position to take a look at the publishing, administration and sale
of particular person merchandise by ID, after which over time configure the router with
progressively an increasing number of product varieties, primarily rising the
share of merchandise dealt with by the brand new resolution.
When all merchandise have been being dealt with by the brand new methods, the legacy
Integration Middleware was decommissioned, realising the numerous £
saving in license, help and datacenter internet hosting charges.
Altering the organisation to permit this to occur on an ongoing foundation
Our groups had already been working with the consumer, in one other a part of the organisation and had already
efficiently displaced a special legacy system.
At an engineering degree throughout the organisation steady supply and good supporting high quality practices
have been now the established norm, and a microservices type structure enabled common and impartial deployment
of containerised providers onto a cloud primarily based platform.
The groups on the brand new programme, working with new stakeholders, wanted to take this different a part of the enterprise
on the identical “agile and CD” journey, and early threat managed releases enabled belief to be earned. Over time it
was potential to display how new engineering and high quality practices together with CD have been mitigating the identical
dangers that had traditionally resulted in increased ranges of forms and governance. So much less frequent,
bigger scope releases have been additionally displaced by smaller, extra frequent, increased confidence deployments, and
toggled releases to the enterprise once they have been able to tackle the modifications.
Closing ideas
After all there was considerably extra complexity and
integration necessities than implied by the simplified story above. An instance
of the necessity for Archeology launched itself shortly after testing the
new implementation in manufacturing. Plenty of enterprise vital administration
data reviews didn’t tally – merchandise have been “getting misplaced”.
After a lot digging the staff discovered that the database utilized by the
Integration Middleware (for storing the state of lengthy operating enterprise
transactions) was replicated to the organisation’s knowledge warehouse. By way of a quantity
batch jobs, saved procedures and views this knowledge was made accessible to be used
throughout the enterprise vital KPI reviews.
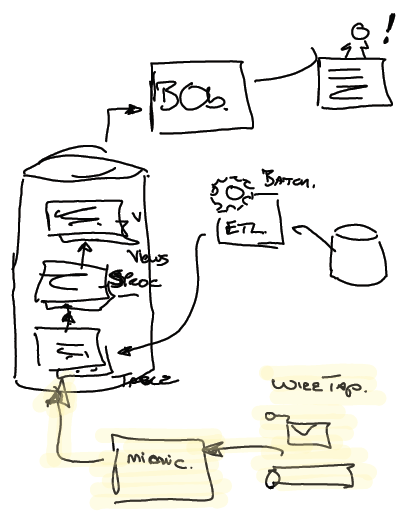
Further Legacy mimics have been required to make sure that these reviews
didn’t break. The staff used a
Wire Faucet on
gross sales messages coming from the Retailer Entrance and utilizing JDBC injected the info into
acceptable tables throughout the knowledge warehouse. These extra mimics
additionally grew to become a part of the transitional structure, and can be eliminated when
potential.
The strategy of department by abstraction, and use of patterns and practices
described above was one meant to decrease threat.
Utilizing Occasion Interception (technical seam), Legacy Mimics and Transitional Structure
enabled the consumer to interrupt the issue up. Then segmenting by product (enterprise seam),
on this case product sort, enabled tremendous management of the broader rollout and additional administration of threat.
General the strategy allowed the enterprise to proceed with the system substitute on the tempo that was
comfy to them.
The strategy allowed threat to be managed, however got here at a value. A query to think about is subsequently
“What worth does the enterprise place on this threat mitigation?” Being express and quantifying it, will enable
a staff to trace investments towards it.
The occasion router and legacy mimics have been a part of an funding in a transitional structure meant to handle
threat. Their roles have been to create choices enabling threat to be managed. It may be very simple for such work to be
seen as “throw away” – and as such a value to be averted wherever potential. Be express and clear on this
“worth of threat mitigation” vs “price of transitional structure” trade-off.
[ad_2]